📋 Table of Contents
Introduction
In today's rapidly evolving digital landscape, traditional security models are failing to protect organizations against sophisticated cyber threats. The concept of a secure network perimeter has become obsolete as employees work from anywhere, applications move to the cloud, and data flows across multiple platforms and devices.
As a Solution Architect working with organizations across the DACH region and broader European Union, I've witnessed firsthand the transformation that Zero Trust security frameworks can bring to businesses of all sizes. This comprehensive guide will help you understand what Zero Trust really means, why it's essential for modern organizations, and how to begin your Zero Trust journey with Microsoft 365.
What is Zero Trust?
The Core Principle
Zero Trust is a security framework built on the principle of "never trust, always verify." Unlike traditional security models that assume everything inside the corporate network is trustworthy, Zero Trust assumes that threats can come from anywhere—both inside and outside the organization.
This approach requires verification of every user, device, and application attempting to access resources, regardless of their location or previous access history. Every access request is treated as if it originates from an untrusted network, requiring authentication, authorization, and continuous validation.
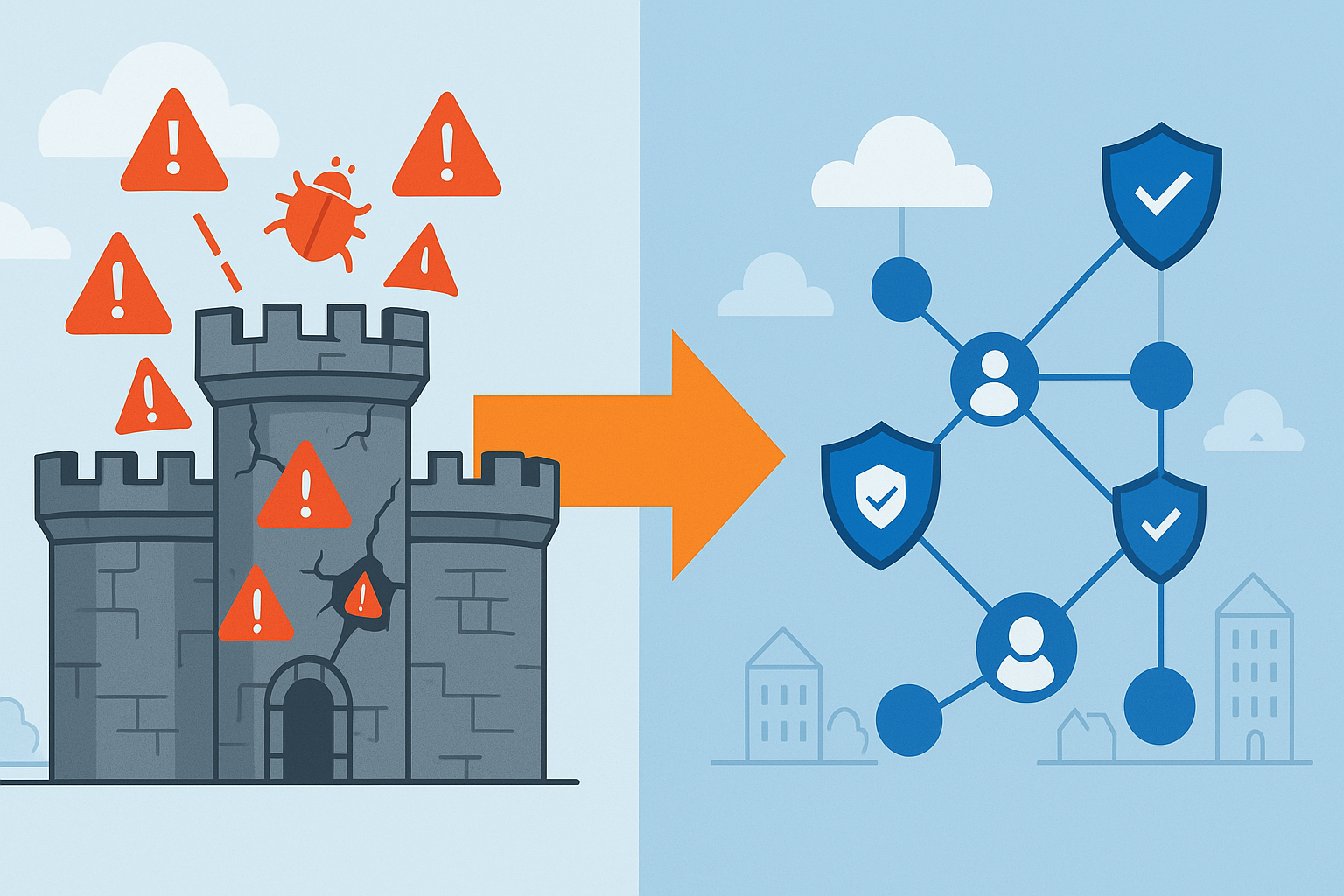
From Perimeter to Identity-Centric Security
Traditional security models relied heavily on network perimeters—firewalls, VPNs, and network segmentation—to create a "trusted" internal environment. However, this castle-and-moat approach has several critical weaknesses:
- Lateral Movement: Once attackers breach the perimeter, they can move freely within the network
- Insider Threats: Malicious or compromised internal users have broad access to resources
- Cloud Adoption: Resources and data no longer reside within a defined perimeter
- Remote Work: Users access resources from various locations and devices
Zero Trust addresses these challenges by shifting focus from network-centric to identity-centric security, where every access decision is based on the identity of the user, the health of the device, and the sensitivity of the resource being accessed.
Microsoft's Six Zero Trust Pillars
Microsoft has structured Zero Trust around six fundamental pillars, each addressing a critical aspect of modern cybersecurity. Understanding these pillars is essential for implementing a comprehensive Zero Trust strategy.
1. Identities
Identity serves as the foundation of Zero Trust security. Every user, service account, and application must be verified and continuously validated throughout their session.
Key Components:
- Multi-Factor Authentication (MFA): Requiring multiple forms of verification
- Conditional Access: Risk-based access policies
- Identity Protection: Detecting and responding to identity-based threats
- Privileged Access Management: Securing administrative accounts
2. Devices
Device security ensures that only healthy, compliant devices can access corporate resources, regardless of ownership or location.
Key Components:
- Device Compliance: Ensuring devices meet security standards
- Mobile Device Management (MDM): Managing corporate and personal devices
- Endpoint Detection and Response (EDR): Monitoring and responding to device threats
- Device Health Attestation: Verifying device integrity
3. Applications
Application security focuses on discovering, managing, and securing all applications within the organization, including cloud apps, on-premises applications, and shadow IT.
Key Components:
- Cloud App Security: Discovering and managing cloud applications
- Application Proxy: Secure access to on-premises applications
- API Protection: Securing application programming interfaces
- Application Governance: Managing application permissions and access
4. Data
Data protection ensures that sensitive information is classified, labeled, and protected throughout its lifecycle, regardless of where it resides or how it's accessed.
Key Components:
- Information Protection: Classifying and labeling sensitive data
- Data Loss Prevention (DLP): Preventing unauthorized data sharing
- Rights Management: Controlling access to protected documents
- Data Governance: Managing data lifecycle and compliance
5. Infrastructure
Infrastructure security applies Zero Trust principles to on-premises and cloud infrastructure, ensuring that all systems are properly configured, monitored, and protected.
Key Components:
- Cloud Security Posture Management: Monitoring cloud configurations
- Infrastructure as Code: Securing automated deployments
- Vulnerability Management: Identifying and remediating security weaknesses
- Network Segmentation: Limiting lateral movement
6. Networks
Network security in Zero Trust focuses on encrypting communications, implementing microsegmentation, and monitoring network traffic for threats.
Key Components:
- Network Access Control: Controlling device network access
- Microsegmentation: Creating secure network zones
- Encrypted Communications: Protecting data in transit
- Network Monitoring: Detecting suspicious network activity
Why Zero Trust Now?
The Changing Threat Landscape
Cyber threats have evolved significantly in recent years, becoming more sophisticated, targeted, and damaging. Traditional security approaches are struggling to keep pace with these evolving threats:
- Advanced Persistent Threats (APTs): Long-term, stealthy attacks that can remain undetected for months
- Ransomware: Increasingly sophisticated attacks targeting critical business operations
- Supply Chain Attacks: Compromising trusted vendors to access target organizations
- Insider Threats: Malicious or negligent employees with legitimate access
Digital Transformation Drivers
Several key trends are driving the need for Zero Trust security models:
Cloud Adoption
Organizations are rapidly moving applications and data to cloud platforms, eliminating traditional network boundaries. This shift requires new security approaches that don't rely on network perimeters.
Remote Work
The COVID-19 pandemic accelerated remote work adoption, with many organizations now supporting permanent hybrid work models. Employees access corporate resources from various locations, devices, and networks, making traditional VPN-based security insufficient.
Mobile and BYOD
The proliferation of mobile devices and bring-your-own-device (BYOD) policies has expanded the attack surface. Organizations must secure corporate data on devices they don't fully control.
IoT and Edge Computing
Internet of Things (IoT) devices and edge computing are creating new endpoints that need to be secured and managed, often in environments where traditional security controls are impractical.
DACH Region Perspective
Regulatory Compliance
Organizations in the DACH region (Germany, Austria, Switzerland) face stringent regulatory requirements that make Zero Trust particularly valuable:
GDPR Compliance
The General Data Protection Regulation (GDPR) requires organizations to implement appropriate technical and organizational measures to protect personal data. Zero Trust principles align well with GDPR requirements:
- Data Minimization: Zero Trust's principle of least privilege access
- Privacy by Design: Built-in data protection controls
- Accountability: Comprehensive audit trails and access logging
- Data Subject Rights: Enhanced visibility and control over personal data
NIS2 Directive
The updated Network and Information Security (NIS2) Directive, which came into effect in 2023, requires enhanced cybersecurity measures for critical infrastructure and important entities. Zero Trust helps organizations meet these requirements through:
- Comprehensive risk management frameworks
- Incident detection and response capabilities
- Supply chain security measures
- Regular security assessments and reporting
German Business Culture and Zero Trust
German business culture values thoroughness, quality, and systematic approaches—characteristics that align well with Zero Trust implementation:
Gründlichkeit (Thoroughness)
The German concept of thoroughness supports comprehensive Zero Trust implementation across all six pillars, rather than piecemeal security solutions.
Quality Focus
German organizations' focus on quality aligns with Zero Trust's emphasis on continuous verification and improvement of security posture.
Risk Management
German businesses traditionally have strong risk management practices, which provide a solid foundation for Zero Trust risk-based access policies.
Building the Business Case
Cost of Security Breaches
The financial impact of security breaches continues to grow, making the business case for Zero Trust increasingly compelling:
Direct Costs
- Incident Response: Investigation, containment, and remediation costs
- Regulatory Fines: GDPR fines can reach 4% of annual global turnover
- Legal Costs: Litigation and legal representation expenses
- Notification Costs: Customer and regulatory notification requirements
Indirect Costs
- Business Disruption: Operational downtime and lost productivity
- Reputation Damage: Loss of customer trust and brand value
- Customer Churn: Customers leaving due to security concerns
- Competitive Disadvantage: Loss of market position
Zero Trust ROI
Organizations implementing Zero Trust typically see return on investment through:
Risk Reduction
- 50% reduction in security incidents
- Faster threat detection and response
- Reduced impact of successful attacks
- Lower cyber insurance premiums
Operational Efficiency
- Simplified access management
- Reduced help desk tickets
- Automated security processes
- Improved user productivity
Compliance Benefits
- Streamlined audit processes
- Automated compliance reporting
- Reduced compliance costs
- Faster regulatory response
Getting Started with Zero Trust
Assessment and Planning
Before implementing Zero Trust, organizations need to understand their current security posture and develop a comprehensive implementation plan:
Current State Assessment
- Identity Management: Evaluate existing authentication and authorization systems
- Device Inventory: Catalog all devices accessing corporate resources
- Application Portfolio: Identify all applications and their security requirements
- Data Classification: Understand what data you have and where it resides
- Network Architecture: Map current network topology and security controls
Gap Analysis
Compare your current state against Zero Trust requirements to identify gaps and prioritize improvements.
Microsoft 365 as Your Zero Trust Foundation
Microsoft 365 provides an excellent foundation for Zero Trust implementation, especially for organizations already using Microsoft technologies:
Business Premium Benefits
- Azure AD Premium P1: Conditional access and identity protection
- Microsoft Intune: Device management and compliance
- Microsoft Defender for Business: Endpoint protection
- Information Protection: Data classification and labeling
E5 Security Advanced Features
- Azure AD Premium P2: Advanced identity protection and PIM
- Microsoft Defender for Cloud Apps: Cloud app security
- Microsoft Defender for Identity: On-premises identity protection
- Advanced Threat Protection: Email and collaboration security
Implementation Phases
Zero Trust implementation should follow a phased approach:
Phase 1: Foundation (Weeks 1-4)
- Enable multi-factor authentication for all users
- Implement basic conditional access policies
- Begin device enrollment and compliance
- Establish security monitoring
Phase 2: Enhancement (Weeks 5-12)
- Deploy advanced conditional access policies
- Implement data classification and protection
- Enhance endpoint security
- Integrate cloud applications
Phase 3: Optimization (Weeks 13-24)
- Deploy advanced threat protection
- Implement privileged access management
- Enhance monitoring and analytics
- Continuous improvement and optimization
Conclusion
Zero Trust represents a fundamental shift in cybersecurity thinking, moving from perimeter-based security to identity-centric protection. For organizations in the DACH region and broader EU, Zero Trust offers significant benefits in terms of regulatory compliance, risk reduction, and business enablement.
The key to successful Zero Trust implementation is understanding that it's not a destination but a journey of continuous improvement. By starting with Microsoft 365 as your foundation and following a phased implementation approach, organizations can achieve significant security improvements while maintaining user productivity and business agility.
Next Steps
Ready to begin your Zero Trust journey? Consider these immediate actions:
- Assess Your Current State: Evaluate your existing security posture across the six Zero Trust pillars
- Develop Your Strategy: Create a comprehensive Zero Trust implementation plan
- Start with Quick Wins: Implement MFA and basic conditional access policies
- Engage Stakeholders: Build support across your organization
- Seek Expert Guidance: Work with experienced solution architects and consultants
About the Author
Philipp Schmidt is a Solution Architect at farpoint.tech, specializing in Microsoft 365 Zero Trust implementations for organizations across the DACH region and broader European Union. With extensive experience in cybersecurity, compliance, and digital transformation, Philipp helps organizations navigate the complexities of modern security challenges while enabling business growth and innovation.
Expertise: Zero Trust Architecture, Microsoft 365 Security, GDPR Compliance, Identity and Access Management, Cloud Security
Contact: farpoint.tech | 365zerotrust.de